In many of my articles I talked about how to make your WordPress website hosted from home via your Synology NAS more secure. Today I want to have a more in depth conversation about the security that can come from the union of the RT2600ac, MR2200ac or RT6600ax Synology router and your Synology NAS in the same network environment, a union that has nowadays become mandatory, and I’ll explain why. For those of you not yet familiar with the Synology Router, it has a powerful operating system called SRM, graphically very similar to your Synology DSM.
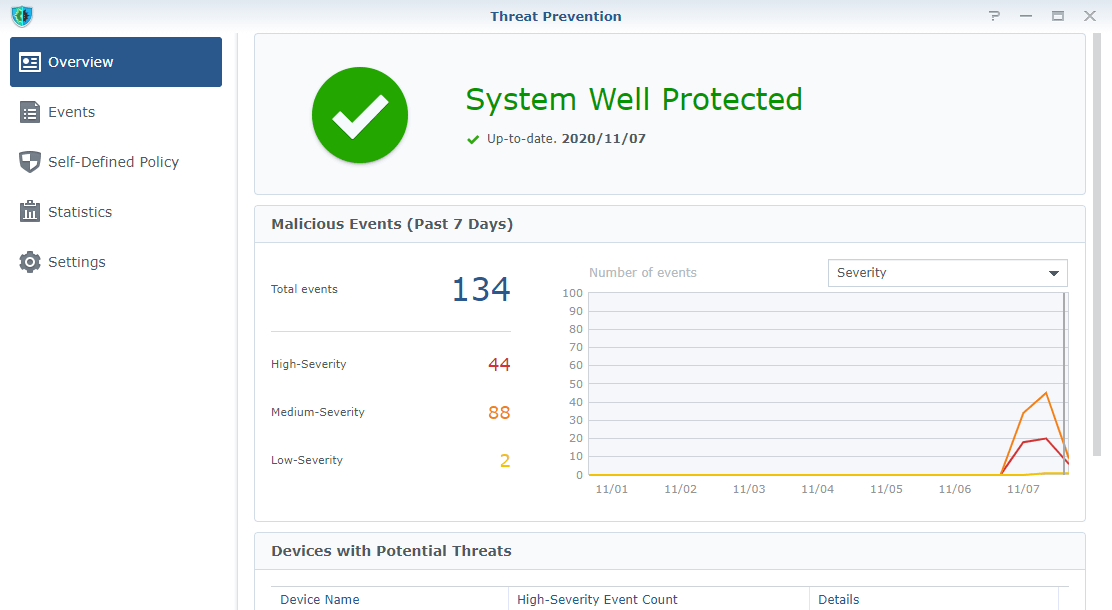
The powerful SRM operating system combined with the package called “Threat Prevention” make an unmatched duo. Utilizing business-grade intrusion prevention technology, the Threat Prevention package inspects the incoming and outgoing traffic of your network and blocks malicious packets from passing through. Threat Prevention is signature-based. It monitors incoming and outgoing traffic using Deep Packet Inspection (DPI) – not just checking the domain or IP – and is able to drop any malicious packet detected in real time. Threat Prevention signature and database updates take place daily automatically.
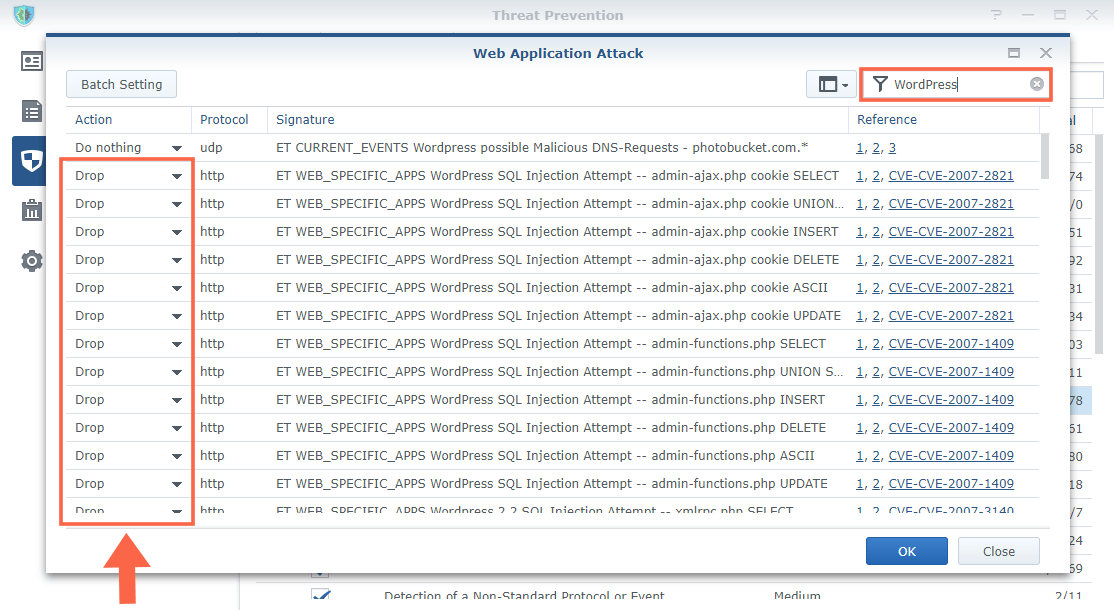
As you can see in the screenshot below, after I set up my Threat Prevention package, I activated the Web Application Attack protection to protect my WordPress website hosted on my Synology NAS.
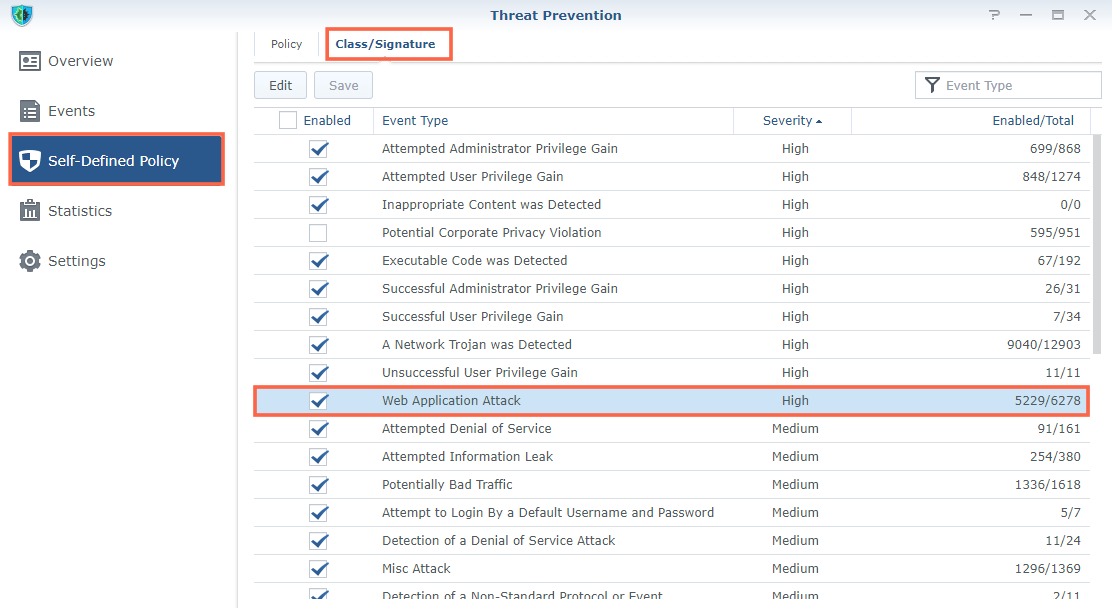
All malicious attacks on my WordPress website hosted on my Synology NAS are automatically blocked by Threat Prevention in real time. We are talking about different attacks such as file modification attempts, WordPress administration intrusion attempts, SQL Injection, intrusion attempts favored by old plugins etc.
What is SQL Injection? SQL Injection is a code injection technique that might destroy your WordPress database. SQL Injection is one of the most common web hacking techniques. SQL Injection is the placement of malicious code in SQL statements, via web page input.
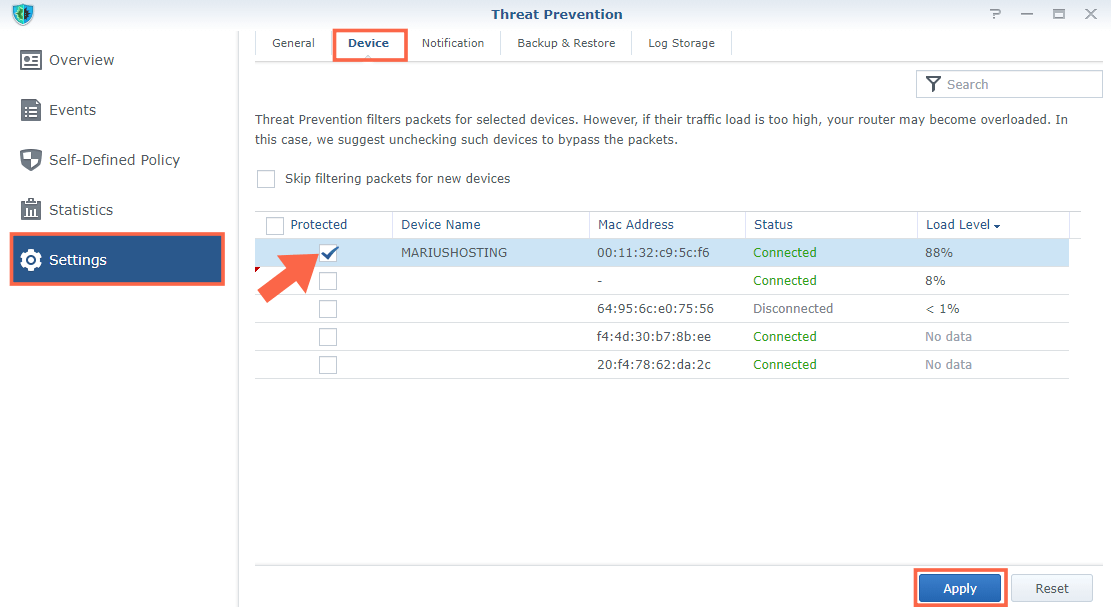
In setting up my Threat Prevention application I made sure that the NAS on which mariushosting.com is hosted is correctly inserted in the Devices to be protected.
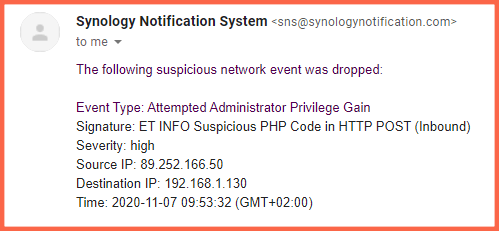
When an “intruder” is blocked, notifications are received via email or SMS and the various logs are saved in your SRM operating system. You can easily decide which notifications to receive and which not to receive, the interval between one notification and another etc.
Note: Whether you use Synology’s WordPress package or the official WordPress package downloaded from wordpress.org (which I recommend), know that your website will be 100% protected by Threat Prevention.
Note: How to Speed Up Threat Prevention.
Note: Not only WordPress is protected, but all web applications hosted on your Synology NAS. For example, if you host a Joomla website on your Synology NAS, just activate the Web Application Attack protection to be automatically protected.
Note: Threat Prevention is also able to block different PHP CVE. So if you run an old PHP version, for example PHP 7.2 on your Synology NAS, having Threat Prevention in your router will protect you when new CVE are discovered, in real time. What is CVE? Common Vulnerabilities and Exposures.
Note: Threat Prevention signature and database updates take place daily automatically.
Note: If you have thought about using your Synology NAS as a web server, a Synology router also becomes mandatory to make your business more secure.
This post was updated on Monday / July 10th, 2023 at 11:06 AM
